Intro
This article will take a detailed look at what the term build-info is all about and why it will help us protect against attacks such as the Solarwinds Hack.
In the past two years, we have had to learn a lot about cybersecurity. The new attack vectors are becoming more and more sophisticated and are directed more and more against the value chain in general. But what does that mean for us? What can be done about it, and what reactions have the state already taken?
Intro:
In this post, we’re going to look at the differences between the various cybersecurity defence techniques. Here you can identify four main groups, which we will go through briefly one after another to illustrate the advantages and disadvantages.
Intro # Again and again, we read something in the IT news about security gaps that have been found. The more severe the classification of this loophole, the more attention this information will get in the general press. Most of the time, you don’t even hear or read anything about all the security holes found that are not as well known as the SolarWinds Hack, for example. But what is the typical lifeline of such a security gap?
In this episode, I’ll show you how to make a comfortable bushcrafting chair out of a few sticks and a little string.
Step 1 - Finding suitable wood # For this seat, we need three wooden poles. These must be stable enough to bear the weight of whoever wants to sit on them. When choosing the pieces of wood, you should, as always, make sure that only dead wood is used. In addition to the aspect of not damaging living trees, it also has a convenient background. With fresh wood, you always have to expect that there is still some moisture and resin in the workpiece and leak out in different places over time. In my search, I opted for secluded beech wood. All bars have a diameter of approx. 10cm are dry and sufficiently stable to hold my weight individually. Of course, rotten wood is not advisable.
Intro # What is the Common Vulnerability Scoring System short called CVSS, who is behind it, what are we doing with it and what a CVSS Value means for you? I will explain how a CVSS Score is calculated, what the different elements of it mean and what are the differences between the different CVSS versions.

# When I’m out in the forest, I always enjoy having some tools with me. The backpack is certainly a little heavier, but there are countless possibilities. My son was there again on one of my last tours. At the time I write this blog post (early 2021), he is ten years old. It’s always lovely to see the enthusiasm with which new things are tried.
We had set ourselves the goal of building a bank. We had an axe, a saw and a paracord with us as tools.
To find a suitable workpiece, forest areas in which there are deciduous trees are suitable. Conifers are usually not very ideal because they contain much resin. Now and then, you will find places where some medium-sized trees such as birch, beech or oak have been fallen due to the last storm, are relocated. Of course, you have to be careful in such places whether the tree trunks are still under tension. We found just such a place, and we immediately started to sift through the wood. Since the logs had fallen for some time, it was safe to move between them.
Today we’re going to look at how to make a rocket stove with an axe and a saw.
The construction does not require any other materials such as wire or the like.
This is a variant that can be used to boil water yourself.
Even in wet weather, this variant works very well because, with the correct selection of the workpiece, the inner dry wood is used to generate sufficient embers.
In this construction, the physical effect is used, in which hot air rises faster than the colder ambient air. This is, among other things, the reason why this variant works better the colder the ambient temperature is.
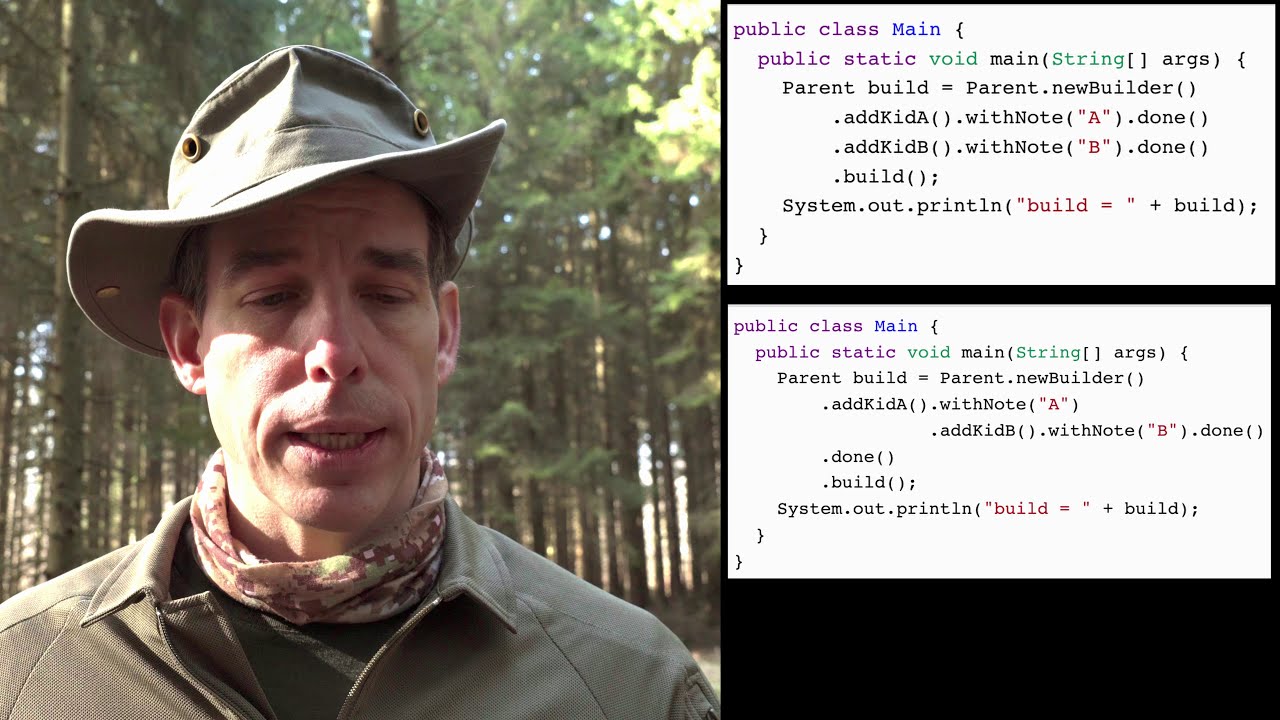
Builder-Pattern # The book from the “gang of four” is part of the essential reading in just about every computer science branch. The basic patterns are described and grouped to get a good start on the topic of design patterns. But how does it look later in use?
Here we will take a closer look at one pattern and expand it.
Intro: # Sometimes you need a small container to catch a little water, hold small things together, or only a temporarily drinking cup. Today we will look at how a makeshift cup can be made from a round wood piece with simple means. All we need is a saw, a knife and a little paracord. But one thing at a time. Let’s start by choosing the right piece of wood.
Intro
In this article, we will look at the difference between the inheritance and delegation concepts. Or, to put it better, why I prefer delegation and why I want to emphasize this rarely-used feature in Java.
The four factors that are working against us # Software development is more and more dependent on Dependencies and the frequency of deployments is increasing. Both trends together are pushing themselves higher. Another element that turns the delivery of software into a network bottleneck is the usage of compounded artefacts. And the last trend that is working against us, is the exploding amount of edges or better-called edge nodes.All four trends together are a challenge for the infrastructure.But what we could do against it?