A logbook is a record-keeping tool used in various fields to track information over time. It typically contains entries documenting events, activities, observations, or data related to a particular subject or task. Logbooks can take different forms depending on their purpose, ranging from handwritten notebooks to digital databases.
Discover the hidden dangers of bidirectional control characters! We dive deep into how these essential text-rendering tools can be exploited to manipulate digital environments. Learn about their security risks, from filename spoofing to deceptive URLs, and uncover the crucial strategies to safeguard against these subtle yet potent threats. Understand how to protect your systems in a multilingual world. Join to ensure your digital security is not left to chance!
Audio steganography is a technique for hiding information within an audio file so that only the intended recipient knows of the hidden data’s existence. This method belongs to the broader field of steganography, which itself is a subset of security systems and comes from the Greek words “steganos,” meaning covered, and “graphein,” meaning writing.
Steganography is the practice of concealing a message, file, image, or video within another message, file, image, or video. Unlike cryptography, which focuses on making a message unreadable to unauthorised parties, steganography aims to hide the message’s existence. The word “steganography " is derived from the Greek words “steganos ,” meaning “covered ,” and “graphein ,” meaning “to write.”
What is a winter trekking tour? # A winter trekking tour typically involves hiking or walking through snow-covered landscapes during the winter season. These tours are popular in regions with significant snowfall and mountainous terrain, such as the Alps, the Rockies, the Himalayas, and other mountain ranges worldwide. Winter trekking tours offer adventurers the opportunity to explore stunning winter landscapes, experience the tranquillity of the snowy wilderness, and challenge themselves physically and mentally.
The Bird-Eye View # A Compensating Transaction Pattern is a technique used to ensure consistency when multiple steps are involved in a process, and some steps may fail. It essentially consists in having “undo” transactions for each successful step, so if something goes wrong later on, you can reverse the changes made earlier and maintain data integrity.
Serialisation in Java is implemented to convert the state of an object into a byte stream, which can be quickly persisted to a file or sent over a network. This process is essential for persisting object data, supporting network communication, and facilitating sharing of objects between different parts of a distributed system.
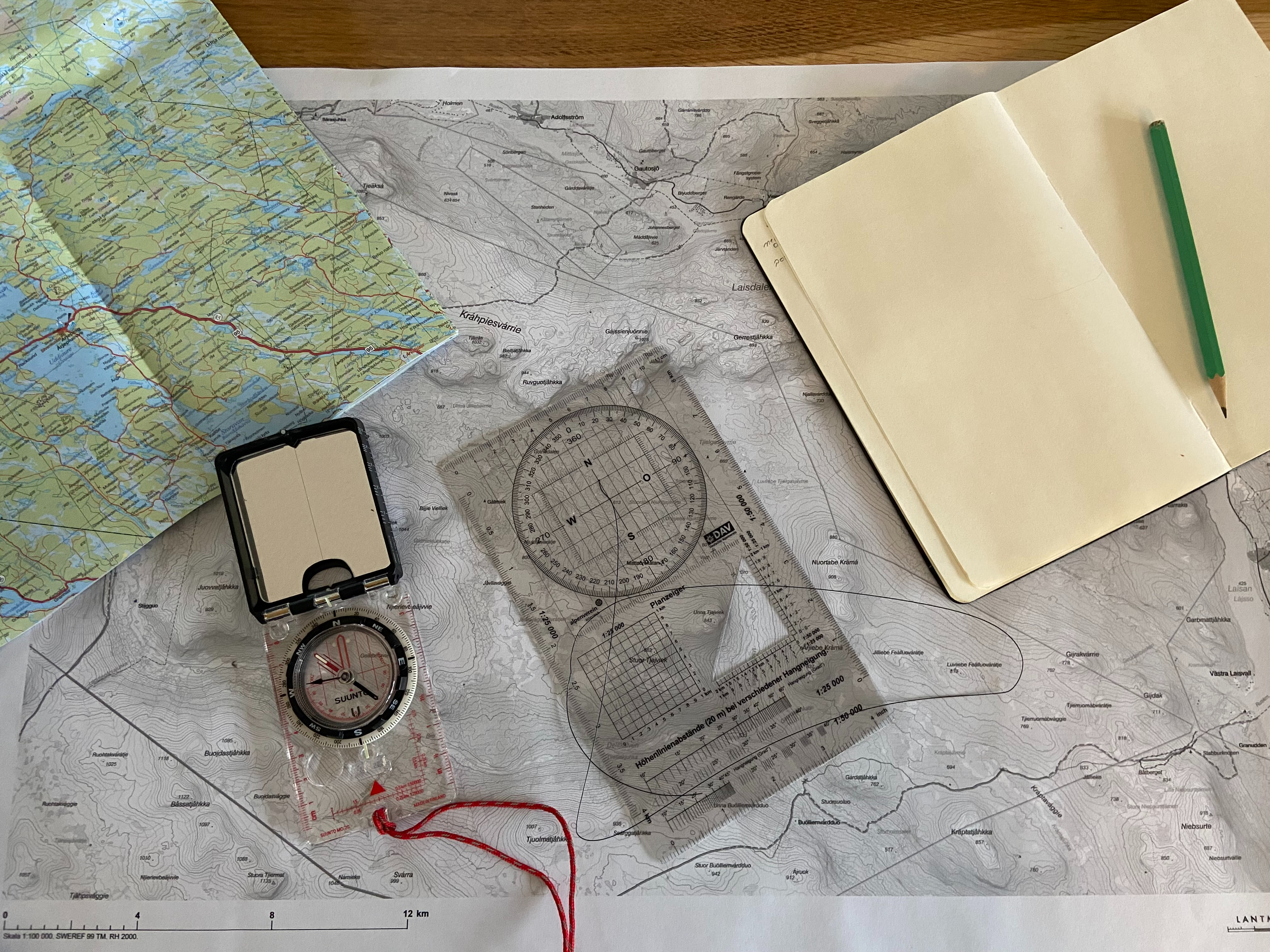
UTMref stands for Universal Transverse Mercator (UTM) reference system. It is a coordinate system to locate positions on the Earth’s surface. The UTM system divides the Earth into a series of zones, each 6 degrees of longitude wide, and assigns a coordinate grid to each zone. This grid system uses easting (measured in meters east of a reference meridian) and northing (measured in meters north of the equator) coordinates to define locations within each zone.
Contextual analysis in cybersecurity involves examining events, actions, or data within the broader context of an organization’s IT environment. It is a critical component of a proactive cybersecurity strategy, aiming to understand the significance of activities by considering various factors surrounding them. This multifaceted approach helps cybersecurity professionals identify and respond to potential threats effectively.
A milliradian (MilRad or mrad) is a unit of angular measurement commonly used in precision shooting, optics, and ballistics. It is based on dividing a circle into 6.283 radians (2π radians), with each radian further divided into 1,000 milliradians. The milliradian is often denoted as “mil.”
CWE stands for Common Weakness Enumeration. It is a community-developed list of software and hardware weakness types that can serve as a common language for describing, sharing, and identifying security vulnerabilities in software systems. CWE aims to provide a standardized way of identifying and categorizing vulnerabilities, making it easier for software developers, testers, and security professionals to discuss and address security issues.